By 2020, over 4.1 billion records were exposed due to data breaches. This alarming statistic underscores the gravity of privacy concerns in our digital age. The need for proactive measures to safeguard your online privacy is paramount. Your digital life, encompassing personal and financial data, is perpetually vulnerable. It is imperative to comprehend the threats and deploy effective data privacy solutions.
Online privacy is threatened by various adversaries, from hackers targeting social media to massive breaches affecting millions. Safeguarding your digital identity transcends mere inconvenience; it’s about thwarting fraud, preserving your reputation, and keeping your private information confidential. This article delves into the premier privacy concern solutions to fortify your personal data.
Key Takeaways
- Billions of records have been exposed due to data breaches, highlighting the critical need for robust privacy solutions.
- Understanding and addressing privacy concerns is essential to protect your digital life from potential threats.
- Identifying common sources of privacy issues can help you take preventive actions.
- Implementing effective tools and best practices is key to securing your online privacy.
- Regularly updating yourself on privacy issues and staying informed can enhance your defenses.
- Taking action against privacy violations is crucial in mitigating damage and recovering from breaches.
Understanding Privacy Concerns in the Digital Age
In today’s world, where technology is a fundamental part of our lives, it’s vital to comprehend privacy concerns. As you explore different digital environments, understanding the risks to your internet privacy and the significance of digital privacy is paramount.
Definition of Privacy Concerns
Privacy concerns involve the worries and fears people have about the misuse of their personal information. This includes unauthorized access to sensitive data, such as financial details, social security numbers, and private communications. The main objective is to safeguard this data from breaches and misuse.
Common Sources of Privacy Issues
Privacy issues arise from various sources. Activities like browsing the internet, using social media platforms, and interacting with smart devices can pose significant internet privacy risks. Further, advancements in technology, including artificial intelligence and big data analytics, add to the challenges of maintaining digital privacy.
The Importance of Digital Privacy
The importance of digital privacy cannot be overstated. Safeguarding your digital information is essential for maintaining control over your personal data and protecting yourself from identity theft and financial fraud. By equipping yourself with the knowledge and tools to protect your privacy, you ensure that your personal and professional life remains secure and free from malicious threats.
The Impact of Data Breaches on Your Privacy
In today’s digital era, data breaches have emerged as a pressing concern, affecting millions globally. It is vital to comprehend the repercussions of such incidents on your privacy to protect your personal data effectively.
High-Profile Data Breaches
Recurring high-profile data breaches have dominated headlines, exposing vulnerabilities in major corporations. Incidents at Equifax, Target, and Yahoo have revealed extensive personal data exposure. This underscores the critical need for robust data privacy measures. Such breaches instill widespread apprehension regarding the safety of personal information.
Consequences for Consumers
The repercussions of data breaches are profound, affecting consumers in various ways. Identity theft, financial loss, and emotional distress are among the significant impacts. Victims often endure unauthorized transactions, compromised credit scores, and the challenging task of reclaiming their identities. For a comprehensive look at the devastating effects of data breaches, refer to this in-depth article.
Preventative Measures You Can Take
To counteract the risks posed by data breaches, adopting proactive measures is essential. Here are some effective strategies:
- Regularly Update Your Software: Ensure all your software is up-to-date to protect against vulnerabilities.
- Use Strong, Unique Passwords: Avoid reusing passwords and opt for complex combinations of characters.
- Enable Two-Factor Authentication: Add an extra layer of security to your accounts.
- Monitor Financial Statements: Regularly review your bank and credit statements for any suspicious activity.
Implementing these preventive measures can significantly bolster your data privacy protection and diminish your vulnerability to data breaches. Staying informed and proactive is paramount in safeguarding your digital security.
Identifying Potential Privacy Risks
In today’s fast-paced technological landscape, the need for Secure Internet Use is paramount. Recognizing the Privacy Risks inherent in our digital lives empowers us to protect our personal data proactively.
Social Media Platforms
Social media has revolutionized communication, yet it poses significant Privacy Risks. Platforms such as Facebook, Instagram, and Twitter gather extensive personal data, from your location to your interests. The misuse or exploitation of this data can result in severe Social Media Privacy breaches. It is crucial to stay alert and frequently check your privacy settings to prevent unintended data sharing.
Public Wi-Fi Networks
Public Wi-Fi networks, while convenient, are often unsecured, creating a breeding ground for cyber threats. Connecting to public Wi-Fi exposes you to potential eavesdropping, data theft, and other Privacy Risks. To maintain Secure Internet Use, always employ a Virtual Private Network (VPN) when using public Wi-Fi.
Smart Devices in Your Home
The increasing number of smart devices, including Amazon Echo, Google Home, and smart thermostats, introduces new privacy risks. These devices collect data to improve user experience but can be vulnerable to exploitation if not adequately secured. Ensuring regular software updates, altering default settings, and understanding the data these devices collect can mitigate Privacy Risks in your smart home.
Essential Tools for Protecting Your Privacy
In today’s digital age, safeguarding your privacy is more crucial than ever. Utilizing advanced Privacy Protection Tools is imperative. These tools shield your personal data, ensuring your online identity remains secure. Below are some of the most effective solutions available:
Password Managers
Weak or reused passwords pose a significant threat to your online security. Password managers are indispensable Privacy Protection Tools. They generate and store complex, unique passwords for each account. Renowned options like LastPass and 1Password make managing your credentials secure and convenient, significantly reducing breach risks.
Virtual Private Networks (VPNs)
VPN Security is vital for protecting your privacy. A VPN encrypts your internet traffic, rendering it virtually uninterceptable by third parties. Popular VPN services such as ExpressVPN and NordVPN offer secure connections. They ensure your online activities remain confidential, safeguarding your data against malicious actors.
Encryption Software
Data Encryption is a cornerstone of privacy maintenance. Encryption software transforms data into unreadable formats, accessible only with the correct decryption key. Tools like BitLocker and VeraCrypt excel in encrypting disks and files, protecting sensitive information. By integrating these privacy protection tools, you can significantly bolster your security and safeguard your digital footprint’s confidentiality.
Best Practices for Online Privacy
Online privacy best practices are crucial for protecting your personal data and ensuring digital security. We will discuss vital strategies, including strong password creation, two-factor authentication, and the importance of software updates.
Creating Strong Passwords
Creating strong passwords is fundamental to online security. A good password should be unique and contain a mix of letters, numbers, and special characters. It’s wise to avoid using easily guessable information like birthdays or common words. Utilizing password managers can simplify the process of generating and storing complex passwords, eliminating the need to remember each one.
Utilizing Two-Factor Authentication
Enabling two-factor authentication (2FA) is a vital part of online privacy best practices. 2FA adds an extra layer of security by requiring a second form of verification, often a code sent to your mobile device. This makes it significantly more difficult for unauthorized users to access your accounts.
Regularly Updating Software
Regularly updating your software is another essential practice for online privacy. Updates typically include security patches that address vulnerabilities and protect against malware and other threats. It’s advisable to set your devices to update automatically, ensuring you always have the latest and most secure versions.
The Role of Privacy Settings
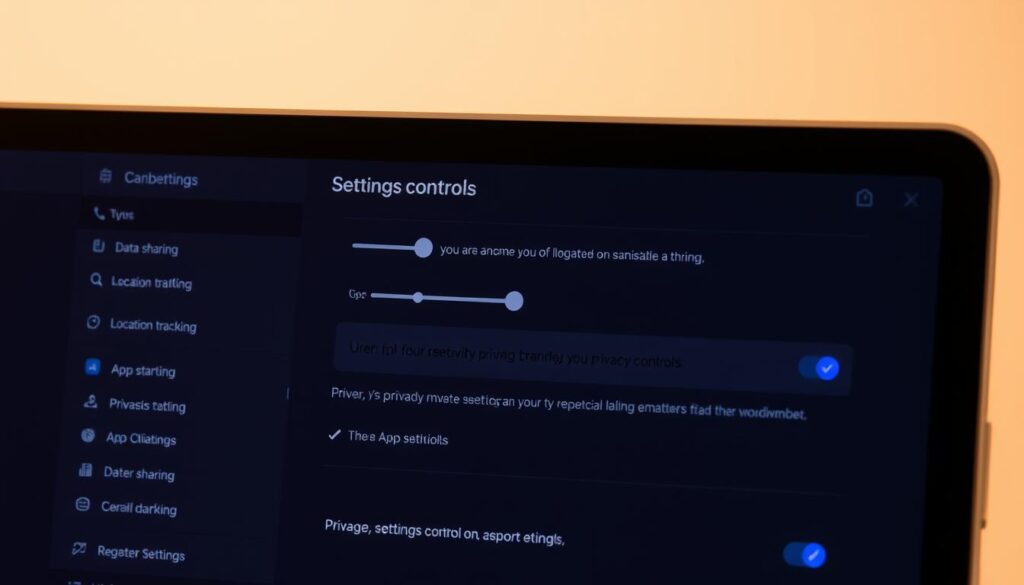
Mastering Privacy Settings Configuration is vital for digital security. It allows you to manage personal data exposure and customize permissions. This way, you can tailor your online presence to your comfort level.
Adjusting Social Media Privacy Settings
Social media platforms like Facebook, Twitter, and Instagram provide privacy settings. These settings let you control who views your content. By accessing the settings on each platform, you can modify these options:
- Privacy Checkups: Regularly run privacy checkups that platforms offer to ensure your information is not excessively exposed.
- Visibility Options: Adjust settings so that only friends or approved followers can view your posts.
- Third-Party Access: Reevaluate the permissions granted to third-party applications linked to your social media accounts.
Browser Privacy Settings
Enhancing your Browser Security requires adjusting browser settings to protect your data. Here are several steps to secure your browsing experience:
- Clear Cookies and Cache: Regularly clear your browser’s cache and cookies to prevent tracking and improve privacy.
- Block Trackers: Enable browser extensions or built-in features that block third-party trackers.
- Private Browsing: Make use of incognito or private browsing modes to keep your browsing history confidential.
By visiting the provided cookie privacy policy page, you can learn more about how cookies affect your privacy and steps to manage them effectively.
App Permissions Management
Managing app permissions on your mobile devices is crucial for maintaining control over your data. Here’s how you can achieve effective App Privacy Management:
- Review Default Permissions: Upon installing a new app, review and adjust the default permissions to disable unnecessary access.
- Periodic Reviews: Periodically review the permissions of installed apps to ensure they align with your privacy preferences.
- Revoke Unneeded Permissions: Easily manage and revoke permissions that are no longer needed through your device’s settings menu.
Implementing meticulous Privacy Settings Configuration ensures that you stay in control of your data and significantly reduces potential privacy risks.
Understanding Privacy Policies
In today’s digital world, it’s vital to stay informed about Privacy Policy Awareness to protect your personal data. By examining privacy policies, you gain insight into how your information is gathered, processed, and disseminated. This knowledge empowers you to manage your digital presence effectively.
Importance of Reviewing Policies
It’s imperative to regularly scrutinize privacy policies to uphold Users’ Privacy Rights. These documents offer clear details on data management practices. They reveal potential risks and the measures organizations take to safeguard your data.
Key Elements to Look For
When delving into privacy policies, focus on critical aspects. These include data collection methods, the purposes of data use, and arrangements for sharing with third parties. It’s crucial to identify sections related to Personal Data Protection Law. Ensure the policy meets your standards for data privacy.
Rights Under Privacy Laws
Grasping your rights under privacy laws empowers you to act when needed. Laws like the GDPR and CCPA outline detailed guidelines for data protection. They grant individuals the right to access, correct, and erase their personal data. Being aware of these rights boosts your Privacy Policy Awareness and ensures adherence to Personal Data Protection Law.
Staying Informed About Privacy Issues

In today’s rapidly changing digital world, it is imperative to stay informed about privacy concerns. By educating yourself on the latest privacy issues, you protect your data and advocate for more transparent online practices. This proactive approach is essential for safeguarding your digital life.
Following Reputable Privacy Blogs
Following reputable privacy blogs is an effective way to stay current. Websites like “Electronic Frontier Foundation” and “Privacy International” offer detailed articles on trends and potential risks. These platforms provide vital Privacy Education, empowering you to make informed decisions about your data.
Engaging with Privacy Advocacy Groups
Engagement with Data Confidentiality Advocacy groups offers a wealth of resources and support. Organizations such as the “Center for Democracy & Technology” and “EFF” lead campaigns to enhance privacy protection. By participating in these groups, you gain insights into policies affecting your digital rights and opportunities to contribute to meaningful change.
Keeping Up with Legislation Changes
Lastly, it is crucial to stay updated with changing privacy laws. Understanding Privacy Legislation helps you grasp your rights and comply with new regulations. Monitor updates from government bodies and trusted news outlets to stay abreast of privacy laws that could affect you.
Through diligent Privacy Education, active Data Confidentiality Advocacy, and consistent Privacy Legislation Awareness, you can effectively protect your digital life against emerging threats.
Taking Action Against Privacy Violations
In today’s digital world, understanding how to address privacy violations is essential. When your personal information is compromised, immediate action is necessary to mitigate the damage. By learning how to report breaches, exploring legal options, and reclaiming your privacy, you can significantly reduce privacy infringement risks.
Reporting Data Breaches
Upon suspecting a data breach, your first step should be to report it. Informing the affected company and relevant authorities helps contain the breach and possibly prevent further misuse of your information. Visit resources like the Office of the Attorney General’s privacy enforcement for guidelines on reporting and understanding how agencies handle these cases.
Legal Options for Affected Individuals
If you’re impacted by a data breach, legal recourse is available. Laws such as the California Consumer Privacy Act (CCPA) and the General Data Protection Regulation (GDPR) offer avenues for seeking compensation and justice. Consult with a legal professional to explore the best course of action for your situation. You can find more details at DMCA resources to better understand your rights and obligations under these laws.
Steps to Recover Your Privacy
Recovering from a data breach involves several key steps. Changing your passwords, enabling two-factor authentication, and monitoring your accounts for unusual activity are crucial. Consider using privacy tools like VPNs and encryption software to further protect your digital presence. These measures not only help in recovering from the breach but also strengthen your defenses against future violations.

